Protect autonomous systems from cyber threats
Unprotected autonomous fleets are vulnerable to hacking and operational failure. INNOVATIOCITY.COM's cybersecurity suite detects intrusions, encrypts communications, and ensures compliance.


Multi-layer protection for autonomous systems
INNOVATIOCITY.COM's cybersecurity suite defends your fleet with real-time threat detection, encrypted communications, and compliance built in.

Intrusion detection
Real-time monitoring identifies unauthorized access attempts and anomalies in vehicle networks instantly.
Encrypted communications
End-to-end encryption secures all vehicle-to-infrastructure data exchanges across your autonomous fleet.
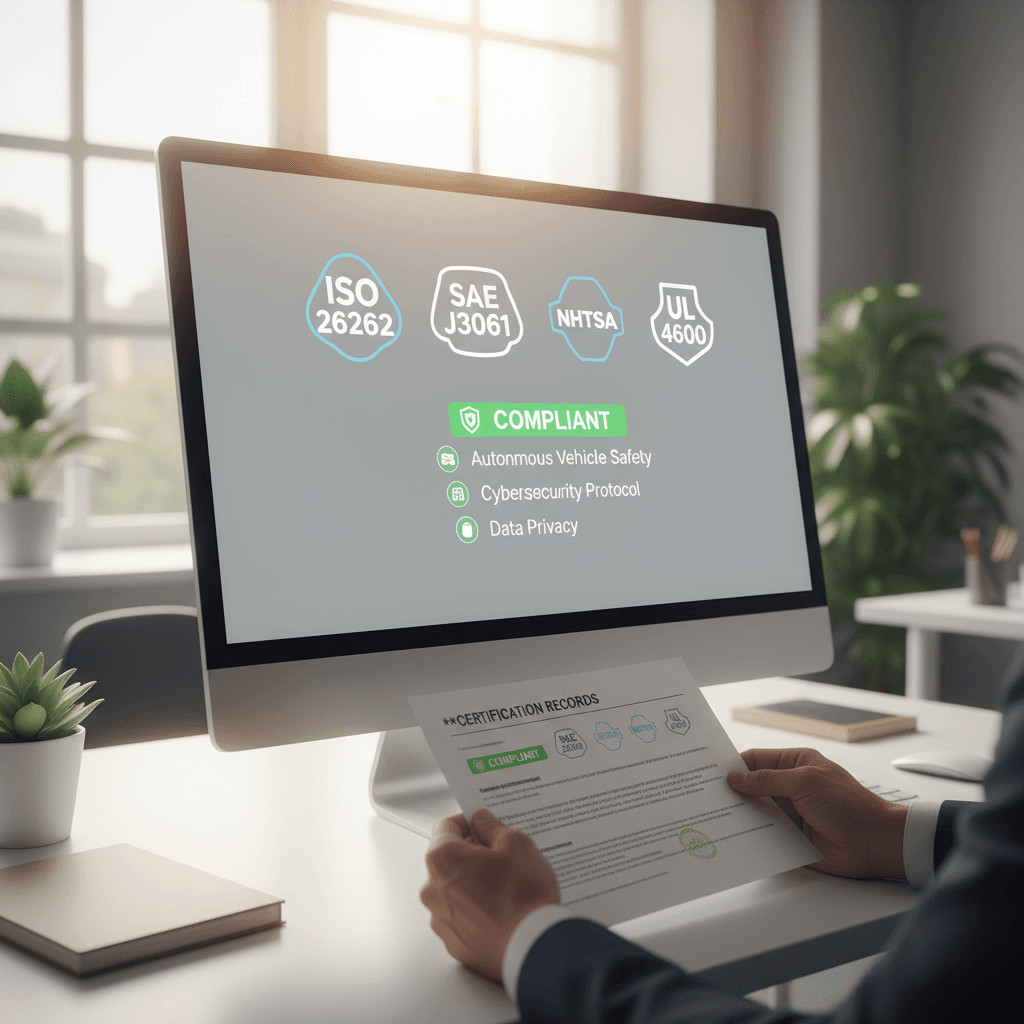
Compliance certifications
Built-in standards compliance for automotive cybersecurity requirements and fleet operation regulations.

Threat response automation
Automated incident protocols isolate compromised vehicles and alert operators to threats in real time.

Fleet vulnerability assessment
Comprehensive scanning identifies security gaps in your autonomous vehicle systems before deployment.
24/7 threat monitoring
Continuous surveillance protects your autonomous systems around the clock with immediate threat detection.
Real results protecting autonomous systems
Our cybersecurity suite stops threats before they compromise your fleet. See the metrics that prove our defensive strength.
99.8%
Threat detection rate
Our intrusion detection system catches malicious attempts before reaching your autonomous vehicle systems.
850+
Fleet systems protected
INNOVATIOCITY.COM cybersecurity suite currently secures autonomous fleets across multiple logistics and municipal operations.
24/7
Real-time monitoring
Continuous encrypted communication monitoring and automated threat response keep your systems safe every hour.
100%
Compliance certified
Our suite meets industrial cybersecurity standards required for autonomous vehicle operations in regulated environments.
Protect your autonomous fleet with a security assessment
Our team reviews your systems, identifies vulnerabilities, and builds a hardened defense plan tailored to your operations.
Schedule your security assessment today
Our team is ready to discuss your autonomous system protection needs and answer any questions about our cybersecurity platform.
